Common Sense Security: Practical Steps for Securing Your Homeless Management Information System (HMIS)

HMIS Security Is More Critical Than Ever
Highly Sensitive Information From Already Vulnerable Populations
An HMIS contains highly sensitive medical, financial, and personal data ranging from substance abuse treatment and mental health records to immigration status. In a world rife with cyberattacks, such private information must always be treated as at risk—especially for already vulnerable populations experiencing homelessness.
Data breaches come with significant safety and security risks. For example, stolen information can worsen the financial situation of people experiencing homelessness, while knowing other people have acquired private life details without consent can undermine a person’s feelings of safety and autonomy.
To protect individuals against privacy violations and data security breaches, all HMISs are subject to HIPAA, 42 Code of Federal Regulations (CFR) Part II, and other regulations. For instance, HIPAA is a federal law requiring that no sensitive health information be disclosed without a patient’s consent or knowledge.
A Trust-Based System
An HMIS is a trust-based system. In other words, clients are putting a great deal of faith into the hands of care providers and case managers when they share the private details of their lives with them.
Most Continuums of Care (CoCs) rely primarily on self-reported data from clients. Individuals experiencing homelessness who don’t trust the security and privacy of an HMIS may be reluctant to answer candidly, which ultimately hinders their ability to get the tailored help they may need - and may also undermine the reliability of your data. Caseworkers know success with clients hinges on trust.
Furthermore, other systems of care such as healthcare, law enforcement, and first responders operate in highly regulated environments and may be reluctant to share information with potentially insecure systems.
A Growing, Rapidly Advancing Threat
Cyberattacks are occurring at a greater frequency and sophistication than ever before. A rapid uptick in ransomware and other attacks has created growing urgency to improve security—hence the expansion of organizations using data security software such as SolarWinds and Kaseya, to name two.
The rise of remote work, while plentiful in benefits, has made data security an increasing priority for organizations, as well.
New threats and heightened risks require CoCs to take a fresh look at security controls and determine whether their current HMIS is maximally secure.
HUD Requires Better Data Security
In addition to CoCs’ deep concern for clients and their motivation to improve the lives of vulnerable populations within their broader community is the issue of compliance. HUD requires serious data protection.
CoCs must adhere to the HMIS Proposed Rule, which mandates uniform technical requirements, proper data collection and database maintenance, and confidentiality of information.
Furthermore, according to the 2004 HMIS Data and Technical Standards Notice, data collection is standardized “nationally and allows local CoCs to generate consistent reports on the characteristics of homeless persons”—ensuring data is collected and safeguarded.
The Notice is primarily about establishing secure consultation among several key groups, including “federal agencies implementing homeless programs, State and local governments, and Continuum of Care agencies experienced in implementing an HMIS, major advocacy groups, and leading academic and national experts on homelessness.”
Put simply, it’s incredibly difficult to be an effective, trustworthy CoC without an HMIS that meets strict data security standards.
Security & Privacy: A Checklist for HMIS System Administrators
Considering the importance of safeguarding clients’ data in a rapidly evolving threat landscape, you definitely don’t want to rely on the bare minimum of data security features. Instead, you should look for an HMIS vendor standing at the front lines of data protection.
Therefore, as you review your current HMIS vendor, or select a new one, to determine their capacity to maintain effective and appropriate security practices, you’ll want to consider how well they align with Systems and Organizations Control 2 (SOC 2).
Developed by the American Institute of Certified Public Accounts, Systems and Organizations Control 2 (SOC 2) is a voluntary compliance standard that guides how organizations ought to manage their data. SOC 2 entails just about everything from Coordinated Entry data to job descriptions and administrative reports for HUD.
Here’s a checklist to ensure your HMIS provider is SOC 2 compliant:
Multi-Factor Authentication: This enables system administrators to supplement standard user credentials with a rolling-code-based, two-factor authentication requirement for added security—and, when necessary, to limit access at the device level.
Password Policy Enforcement: This automatically requires policies around password complexity, maximum login attempts, self-service recovery, and other password settings.
Encryption: Ensure all traffic is 2,048 bit SSL encrypted at transit and at rest. All API traffic should be further AES encrypted, as well.
IP Whitelisting: Customers should be able to opt for staff or agency-level IP whitelisting, requiring each user to log in from a system administrator-defined list of allowed IP addresses.
Detailed Audit Logs: Your HMIS ought to store every change to a client record and offer authorized users a full audit trail of every data field in the system.
Flexible Sharing & Access Controls: These are a combination of system-, project-, user-, and field-level controls that empower system administrators to tailor access to the minimum amount necessary to get the job done.
Physical Controls: A reliable data center employs established best practices for physical access control, including round-the-clock security and technical staff, dual-factor authentication access, biometric scanners, and monitored security cameras.
Client Notification & Consent: Capture and manage client consent and release of information forms directly from the client record, including support for e-signature.
Security Reports: Maintaining a large number of prebuilt security reports or dashboards is vital to data security. Look for an HMIS that also offers customizable reports and dashboards.
HMIS Administrator Support & Privacy Expertise: To stay on top of the constantly changing regulatory and security landscape, your support team should include certified privacy and legal experts, former HUD and federal technical assistance providers, and certified privacy experts (IAPP CIPP/US, CIPT, and FIP certifications).
SOC 2 Certification Gives You Peace of Mind
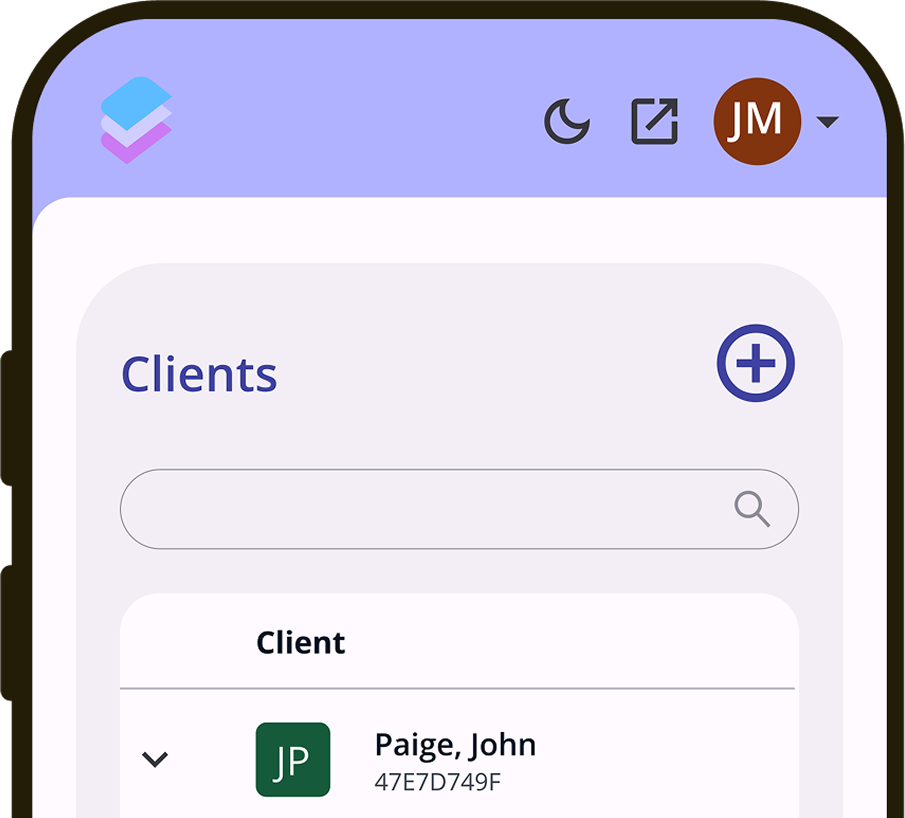
An HMIS built and designed by Bitfocus, Clarity Human Services is SOC 2 certified and has routine audits by external experts, ensuring your data is secure.
These audits address any data integrity concerns and identify what can be done to fix them. Criteria include security, availability, processing integrity, confidentiality, and overall privacy.
The first stage of gaining SOC 2 certification involved an audit focused on data integrity, which was conducted by external experts. Any potential concerns were addressed by Bitfocus. Then, an official SOC 2 auditor conducted a formal audit.
Clarity Human Services is now SOC 2 certified. Maintaining this certification will be an ongoing process that we continue to take seriously.
Clarity is constantly working to maintain data integrity. That’s because an HMIS committed to data security must always be prepared and working toward recertification.
This is the peace of mind SOC 2 certification gives any CoC—keeping your data secure so you can provide the best care and support to the most vulnerable within your community.